Libraries have a responsibility to protect the privacy and confidentiality of patrons. When someone registers in a library, they are required to provide personal identifiable information such as their name, date of birth, address, identification number, phone contact, and email address among other things. With the automation of library services this information is recorded into an electronic database and can be accessed by library personnel. In a library (physical or virtual), the right to privacy is the right to open inquiry without having the subject of one’s interest examined or scrutinized by others.
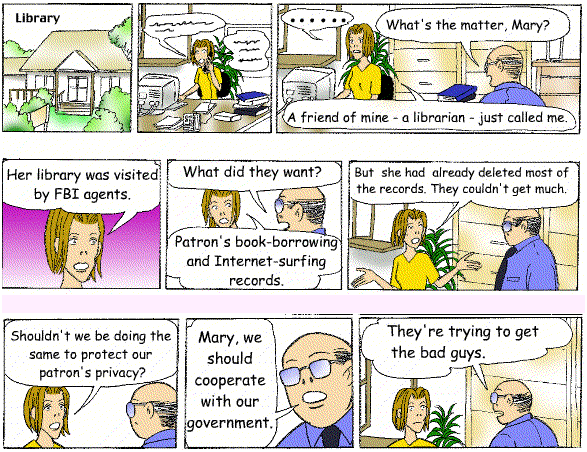
The right of freedom of inquiry also falls under the scope of privacy and confidentiality, as such, records of borrowed books and material, reference queries, internet use should only be kept for as long as it sated in the library’s Privacy Policy. This policy is used to guide staff and library users, and is drafted based upon standard international principles and guidelines such as ALA’s Code of Ethics and the Library Bill of Rights. These declare that a library user’s records and information are confidential, and not subject to disclosure, unless certain conditions are met, such as a user’s consent or the service of a court order.
The development of ICTs has led to an evolution in the types and formats of information that can be accessed and retrieved from a library, and as libraries expand their holdings beyond books to other forms of media and other methods of information access, the pressures on their commitment to protecting the privacy of their patrons have intensified. Libraries are developing ways to deal with this shift by utilizing a range of technologies in their daily operations.
Self Service Self Check MachineS
Some patrons may be ‘shy’ to approach the circulation desk to check-in and check-out controversial or sensitive material, in these instances, self check machines can be utilized. With the use of barcode and RFID technology, these self check machines gives the user a ‘private experience’ (not forgetting to mention skipping long lines).

AUTOMATED SYSTEMS AND ONLINE CATALOGUES
Automated circulation systems track the information of items for many reasons, one such is tracking its usage and popularity. To ensure patron privacy is not compromised, library administrators acquire systems that capture only the minimum data necessary to track who has checked out an item, and ensure it is purged as soon as possible after the item is returned. Additionally, computerized catalogues are configured to not require the identification of the person using it, thus ensuring that patrons’ searches of the catalog remain private.
While it can be fairly simple to protect the identity and privacy records of users with respect to circulation of physical items, such as books and dvd’s, the same can’t be said when using third party electronic resources and the internet. Libraries have seen an increase in the demand for electronic resources such as electronic databases, and access to Internet both wired and wireless (Wi-Fi). In such cases, the implications on users privacy are much more complicated that traditional formats.
INTERNET AND NETWORKED INFORMATION SERVICES
Many subscription databases, such as EBSCOHost require that users log on or otherwise identify themselves, and while the library can ensure that users session history is not saved when in use in the library, they cannot guarantee the same when this service is used externally. Libraries are left in a spin-off when subscribing to these databases, as they cannot dictate the privacy policies of these providers for using patron data. In such cases, an agreement can made between the parties that require the subscription provider to notify the user in each session how and why the data is being collected, and even possibly allow them the option of not having it collected. For more on this you can consult ALAs Library Privacy Guidelines for Vendors.
INTERNET ACCESS AND USER PRIVACY
By far the most demanding aspect of user privacy for libraries come from the internet services they provide to patrons, whether wired or wireless. The internet covers a wide range of information and equally, misinformation. The ALA’s statement on the use of filtering software discourages libraries from using such methods, and stress that the library is a place of inclusion rather than exclusion, and further advises that libraries comply with the law by educating their patrons on the appropriate use of the Internet rather than restricting such use. Libraries while not exclusively censoring the use of the internet, must place restrictions on access to certain content, and are advised to place filtering software at the least restrictive level.
PROTECTING PUBLIC COMPUTERS
Libraries have a ‘duty of care’ to protect the privacy and confidentiality of users data who use their public computers. Many persons who do not have access to a computer and internet utilize the library resources to conduct personal and other transactions, for example, to conduct online banking and shopping, and often personal and sensitive information is communicated over these networks. Some ways in which libraries protect their public computers include:
Installing Antivirus for Computers
adjusting browser settings to not remember history, passwords of users
Disabling third party cookies
Install plug ins that automatically block invisible trackers such as uBlock Origins, and Privacy Badger.
PROTECTING WI- FI NETWORKS
Many libraries provide an open wireless internet access, Wi-Fi, to their users that is not protected, causing privacy issues for information transmitted over the network. Cyber criminals are keen to eavesdrop on these networks and can set up Wi-Fi connections with very legitimate sounding names. Once a user connects to the fraudster’s Wi-Fi, the attacker will be able to monitor the user’s online activity and be able to intercept login credentials, payment card information, and more. The use of Wi-Fi Protected access (WPA) encryption technology is one way to ensure that you are not being snooped on. Here’s how it works-
These are just some of the many issues that libraries face when it comes to protecting the privacy and confidentiality of their users, and the methods and technology used may vary among them.
Can you identify any others? Feel free to share!!!

I find this to be a very interesting read Kazim. Most people underestimate how much data they reveal of themselves and the right they have to protect it. However, in recent events we have seen on news or newspaper articles about data privacy’s being breached or hacked, while providing one significant awareness – that protecting one’s data can preserve their identity.
LikeLike